One beautiful thing about digital transformation is that it has ushered in an era of unprecedented opportunities for universities to innovate in teaching, research, and campus life. However, with this innovation comes elevated risk, dramatically spotlighting the crucial importance of cybersecurity in higher education. With massive amounts of personally identifiable information (PII), intellectual property, and research data housed within institutional systems, universities have become prime targets for cyber adversaries.
Let’s dive deep into the challenges higher education institutions face, the active threats, and the strategies needed to safeguard the integrity and trust of the academic ecosystem.
Why Cybersecurity in Higher Education Is a Priority
- Cyber attacks on schools are on a steep climb
According to Malwarebytes, ransomware incidents in the education sector exploded in 2023. Ransomware attacks on higher education rose 70%, from 68 attacks in 2022 to 116 in 2023, while the broader education sector experienced a 105% surge overall. Another study highlights that nearly two-thirds of education facilities reported cyberattacks in 2024, with attack volumes increasing and ransom demands reaching into the millions. The UK Cyber Security Breaches Survey echoes this trend: 97% of UK universities suffered an attack in 2023, rising to 91% in 2024, with nearly one in four experiencing negative impacts.
- The personal and institutional stakes are enormous
Universities hold deeply sensitive information: student ID numbers, financial records, health data, and groundbreaking intellectual property. A breach can devastate student privacy, institutional reputation, and regulatory compliance, especially under data protection laws like FERPA, GDPR, and others. The University of the West of Scotland’s attack resulted in the exposure of 1 million documents and £14.4 million in financial losses – a sobering reminder of the scale of risk.
Top Data Protection Risks Universities Face
1. Phishing, ransomware, and weak internal controls
Phishing remains the top vector for cyberattacks, 97% of UK institutions reported phishing attempts, with impersonation and malware also ranking high. Ransomware penetration is particularly high in universities: 66% reported ransomware hits in 2024, versus 59% across all industries. Downtime and recovery times are lengthy; 40% of institutions took over a month to fully recover, double the global average.
2. Cloud storage and LMS vulnerabilities
Cloud infrastructure and learning platforms are attractive targets. A breach at Southeast Technological University in November 2024 allowed unauthorised access to bank information and emails. Data leaks from learning management systems (LMS), collaboration tools, virtual classrooms, and mobile apps are growing concerns, often due to misconfiguration, weak API permissions, and unencrypted data flows.
3. Research & IP theft

Beyond student PII, universities host highly valuable research and intellectual property. State-sponsored attacks targeting strategic assets, such as solar car research at Western Sydney University, highlight that motives extend beyond financial gain.
Key Cybersecurity Measures for Educational Institutions
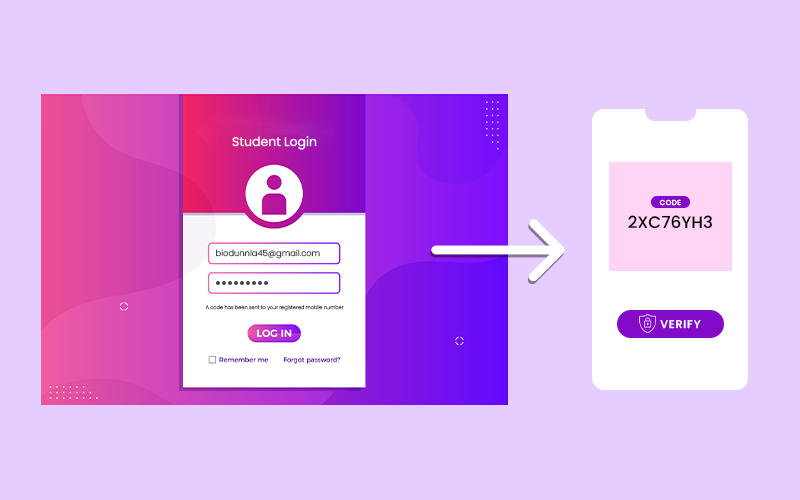
Role-based access control (RBAC), multi-factor authentication, and encryption
Implementing role-based access control can prevent unnecessary data exposure. Pairing this with multi-factor authentication (MFA) drastically cuts credential-based breaches. AES-256 encryption for sensitive data, both in transit and at rest, is essential, aligning with regulatory and best-practice frameworks.
Regular audits and security awareness training
Frequent security audits and penetration tests unearth weak configurations. Yet, 33% of education staff report inadequate IT security, and only 11% increased security awareness after a breach. Training all campus members, faculty, staff, and students to recognise phishing, social engineering, and secure data handling is vital.
Zero‑Trust and Cloud Configuration Monitoring
Zero‑Trust architecture ensures strict identity verification, even within campus boundaries. Organisations like EDUCAUSE recommend adopting zero-trust and continuous monitoring of cloud environments, a key trend for the future of cybersecurity in higher education.
As cyber threats intensified globally, the Massachusetts Institute of Technology (MIT) took a proactive stance by implementing a Zero Trust security framework and AI-powered threat detection tools across its networks. The Zero Trust model, which assumes no implicit trust within or outside the network, ensures that every user or device attempting access is continuously verified. This approach has been especially effective in mitigating insider threats and credential abuse. According to a report from MIT Lincoln Laboratory, this architecture plays a vital role in protecting research and sensitive student data from unauthorised access.
MIT has also leveraged AI-driven analytics to detect unusual activity patterns, such as off-hours access to financial records or mass data downloads, which are red flags for ransomware or data exfiltration attempts. In a 2025 paper, MIT Sloan researchers discussed how integrating machine learning with cybersecurity workflows enabled faster threat detection and response, potentially thwarting an attack that targeted student financial aid systems.
MIT’s layered, tech-forward strategy offers a compelling model for institutions aiming to strengthen cybersecurity in higher education, proving that investment in intelligent tools and policy innovation can pay off in both resilience and reputation.
Student Information Security in Digital Learning Environments
Lurking threats in LMS, virtual classes, and apps
Widespread remote learning has exposed weaknesses: insecure file sharing, accidental data publication, and poorly configured permissions in digital classrooms. Institutions must insist on security features like granular permission controls, SSO integration, and encrypted channels for all EdTech services.
Prioritising secure platforms
When selecting digital learning tools or campus apps, universities should benchmark potential solutions against compliance (FERPA, GDPR), encryption standards, data portability, user control, and transparent data-sharing policies. Vet third-party providers rigorously to avoid introducing vulnerabilities.
Choosing EdTech Tools with Built-in Security
Compliance, encryption, and user control
Key security elements to scrutinise when evaluating EdTech tools:
- Compliance certificates (ISO/IEC 27001, SOC 2, GDPR, FERPA)
- In-transit and at-rest encryption
- Granular user permissions and data ownership flexibility
- Centralised admin oversight and activity logs
- Robust, transparent data retention and deletion practices
Third-party security certifications
Certification stamps (SOC 2, ISO 27001, FedRAMP) and independent security audits demonstrate vendor accountability. Institutions should ask for recent penetration tests and have SLAs that include vulnerability patch timelines.
Building a Cybersecurity Culture on Campus

- Staff training and ongoing awareness
Security isn’t just an IT department task; it’s a shared responsibility. Annual phishing drills, workshop refreshers, and tabletop incident response exercises ensure staff remain vigilant. GDPR and FERPA regulations require mandatory compliance training.
- Data Responsibility Among Students
Cultivate a culture of data responsibility among students, teaching them to:
- Protect personal information online.
- Recognise phishing emails.
- Use secure passwords or password managers.
- Avoid sharing login credentials.
Peer-led cybersecurity clubs or workshops can help normalise these practices.
Partnering with IT Security Providers
Higher-ed institutions are strengthening security by partnering with:
- Managed Detection & Response (MDR) services.
- Cyber-range training providers.
- Public–private partnerships like the UK’s Jisc, which supports institution-wide defences.
These collaborations are vital to bolster limited on-campus IT teams.
Future of Cybersecurity in Education
AI in threat detection
AI-powered monitoring tools can detect anomalies in network behaviour or student record access, improving response times. The 2024 EDUCAUSE Horizon Report affirms AI’s role in fortifying cybersecurity and privacy strategy.
Predictive Analytics for Proactive Defence
Instead of reacting to threats, predictive models enable universities to anticipate them. By analysing threat intelligence, global attack trends, and internal telemetry, institutions can prioritise patching and response planning.
Ransomware threat assessments and cyber-range drills, bolstered with predictive insights, will define next-gen cybersecurity strategies.
Cybersecurity in higher education is more than an IT concern; it’s a vital component of student trust, institutional resilience, and academic integrity. As digital transformation accelerates, attacks become more sophisticated, and regulatory landscapes tighten, universities must elevate cybersecurity to a board-level priority.
By understanding the risks, phishing, ransomware, weak internal controls, and third‑party vulnerabilities, and by implementing robust protections, MFA, encryption, audits, training, and AI-driven analytics, higher education leaders can secure campuses for tomorrow’s learners.
The future of education depends not just on technology, but on trust. Protecting student data is foundational to that trust.

