Cybersecurity in Higher Education: Why It Matters
Thanks to digital advancement and globalisation, universities are no longer passive knowledge repositories. On average, universities host vast networks, research repositories, student portals, learning management systems, cloud platforms, and interconnected services across campuses. However, this growing digital adoption creates a much larger attack surface for institutions. Every endpoint, every student laptop, every IoT sensor, and each cloud instance can be a potential entry point for attackers. For that reason, cybersecurity in higher education is not just a technical concern but a strategic imperative.
And at the heart of the matter lies trust. Students share sensitive personal information, universities conduct research (sometimes commercially valuable or confidentiality sensitive), staff manage financial systems, and institutions collaborate with industry and government. If the data protection fails, trust is lost. Prospective students might hesitate to enrol; funders may demand stronger assurances; regulators will scrutinize compliance. Therefore, the integrity of an institution depends on its ability to safeguard data and systems.
Already, the threats are materializing. Globally, education is one of the most targeted sectors. According to EDUCAUSE, the education sector faces nearly 2,300 cyberattacks per week. Between 2020 and 2021, cyberattacks targeting higher education increased by 75% year over year. Moody’s Ratings recently escalated the cyber risk level for the education sector from “moderate” to “high,” citing institutions’ weaker defences as a driver. In Nigeria and across Africa, many universities are still developing robust cybersecurity frameworks, making them more vulnerable to intrusion and reputational damage. In short, for universities, cybersecurity is not optional; it is critical.
The Biggest Cybersecurity Challenges Facing Universities

Before implementing any solution, institutions must confront the reality of the vulnerabilities they face. Below are some of the most critical challenges in cybersecurity for higher education.
Personal student data targeted by hackers
Universities accumulate deeply personal information, names, addresses, financial records, health data, transcripts, social security numbers, and national IDs. Such data is lucrative to attackers for identity theft, ransomware, or phishing campaigns. In 2024, nearly two-thirds of educational institutions reported having experienced cyberattacks. Breaches in student databases can lead not only to direct harm, but regulatory fines, class action lawsuits, and damage to institutional reputation.
Read more: Harnessing Big Data in Higher Education for Better Student Outcomes
Online exam platforms are vulnerable to cheating and breaches
More universities now run high-stakes examinations, assessments, and proctored tests via digital platforms. These systems, if poorly secured, may allow invaders to tamper with test content, extract questions or answers, or impersonate users. Cheating is one risk; worse is the unauthorized exposure of exam data and credentialing information. The integrity of degrees depends on trust in assessment systems, making this a prime vulnerability.
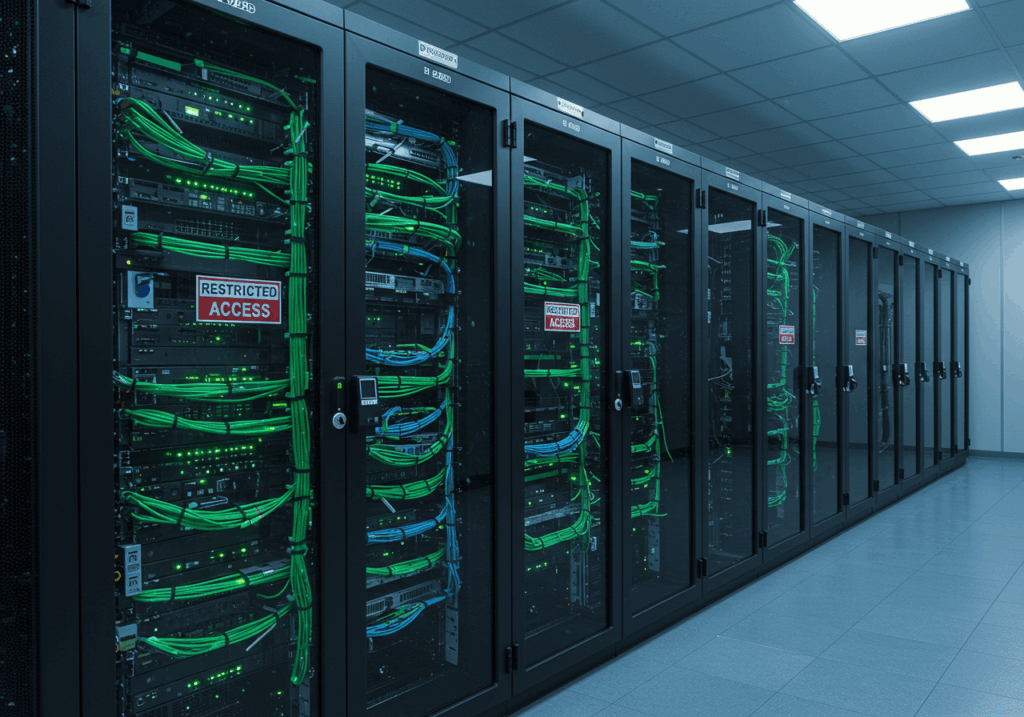
Multi-campus networks and cloud adoption without proper safeguards
Many universities operate across multiple campuses or have satellite locations. Networks stretch across different jurisdictions, with varying local IT practices. Without unified security governance, inconsistencies emerge. In addition, many institutions adopt cloud services rapidly (for storage, collaboration, and research) without a full understanding of shared responsibility models. Misconfigured cloud buckets or APIs, a lack of encryption, or weak access policies can lead to serious breaches. The complexity and scale amplify risk.
Insider threats and lack of role control
Inside institutions, staff, faculty, or even advanced students may have elevated access. If roles and privileges are too permissive, insider misuse, whether deliberate or accidental, can lead to serious breaches. Universities must balance openness (to foster collaboration) and caution (to protect assets).
Legacy systems, budget constraints, and fragmented portfolios
Many universities run aging IT systems, sometimes patched over decades. Legacy infrastructures may have unpatched vulnerabilities or may not support modern security controls. Budget pressures and competing priorities (teaching, research, facilities) often limit the resources allocated explicitly to cybersecurity. Some institutions lack a cohesive strategy; a study of higher education revealed that only about half of institutions had a documented cybersecurity strategy.
Core Cybersecurity Strategies for Higher Education Institutions
Given those challenges, what must institutions do? Below is a set of foundational strategies for strengthening cybersecurity in higher education.
Establish strong password and authentication policies
At the very least, require multi-factor authentication (MFA) for all critical systems. Single passwords alone are too weak in today’s threat landscape. A combination of something you know (password), something you have (token or mobile app), or something you are (biometrics) offers a stronger defence. Enforce complexity rules, limit reuse, and require regular password rotation for less sensitive systems. Consider password vaults or managed credential solutions to reduce user burden and password fatigue.
Data encryption across all devices and platforms
Data must be encrypted in transit and at rest. Whether it is file storage, cloud containers, or backup media, encryption ensures that even if a system is breached, the data remains unintelligible without keys. Universities should implement full-disk encryption on staff and faculty devices as well as encryption for databases, backups, and communications (SSL/TLS, VPNs). Key management must be rigorous and protected.
Role-based access control to minimise insider threats
Implement role-based access control (RBAC) so that access permissions are granted on the principle of least privilege. Users should only have access to data or systems essential for their roles. Periodic review and recertification of permissions help ensure access remains appropriate. For sensitive systems, adopt just-in-time access (temporary elevated privileges) that expire. Logging and auditing of role changes is critical.
Secure network segmentation and zero-trust architecture
Rather than treating the campus network as one monolithic zone, segment networks (e.g., research, administrative, student, guest, IoT). If a breach occurs in one segment, it cannot easily spread. Adopt zero-trust models, where access is continuously verified, regardless of network location. Every request is authenticated and authorized, even from within “trusted” internal networks.
Centralised incident response, monitoring, and logging
Set up a Security Operations Center (SOC) or outsource to a managed security service provider to collect logs, detect anomalies, and respond quickly. Central logging, SIEM (security information and event management) systems, and real-time alerts help detect intrusion early. Define response playbooks, ensure escalation paths, and conduct post-incident reviews.
Backup, disaster recovery, and resilient architecture
Ransomware is a major threat. Having secure, offline, and immutable backups is essential. Backups should be geographically separated, regularly tested, and capable of fast restores. Disaster recovery plans should include failover sites. The goal is resilience: even under attack, mission-critical services can be restored.
Network and endpoint protection
Deploy advanced endpoint protection (EPP/EDR) on all devices. Use intrusion prevention systems (IPS) and next-generation firewalls. Control and monitor inbound and outbound traffic. Whitelist applications when possible and restrict or isolate unknown executables.
Cybersecurity Technologies That Strengthen University Systems
To execute the above strategies, institutions should invest in specific technologies that fit the higher education context.
AI-driven anomaly detection and intrusion prevention
Artificial intelligence and machine learning can parse vast logs and detect anomalies that human analysts might miss. AI-driven systems can identify unusual login patterns, data exfiltration attempts, or lateral movement. According to the 2024 EDUCAUSE Horizon Report, AI-enabled cybersecurity technologies are among the key emerging practices for universities. These systems can reduce dwell time and catch sophisticated attacks early.
Cloud security solutions with compliance built in
Cloud service providers increasingly offer built-in security and compliance controls, such as encryption at rest, identity federation, and data loss prevention (DLP). Universities should choose cloud offerings that align with regulatory requirements (e.g., data location, privacy laws) rather than generic consumer-grade services. Utilize cloud posture management tools to scan configurations, detect misconfigurations, and enforce standards.
Read more: The Role of Cloud Computing in Expanding University Capabilities
Regular system penetration testing and vulnerability scans
Independent penetration testing (internal and external) is vital. Institutions should commission ethical hackers to simulate real-world attacks, uncover weak spots, and report remediation steps. Regular vulnerability scanning (automated) for networks, servers, web apps, and APIs should accompany pen tests. Timely remediation of discovered vulnerabilities is essential.
Intrusion detection/prevention systems and honeypots
Deploy IDS/IPS across network edges and key segments. Use honeypots to attract attackers, gain insight into tactics, and detect breach attempts. This can help sharpen defences, expose tactics, and provide early warnings of new threats.
Security or privacy-enhancing technologies (PETs)
Techniques like homomorphic encryption, differential privacy, and secure enclaves can allow processing of sensitive data without exposing raw values. This is especially useful in research collaborations, where data sharing is needed but privacy must be preserved.
Identity and access management (IAM) with single sign-on
IAM platforms allow central control and single sign-on (SSO) for all institutional systems. Strong identity governance ensures timely onboarding/offboarding, reduces password fatigue, and simplifies access audits and control.
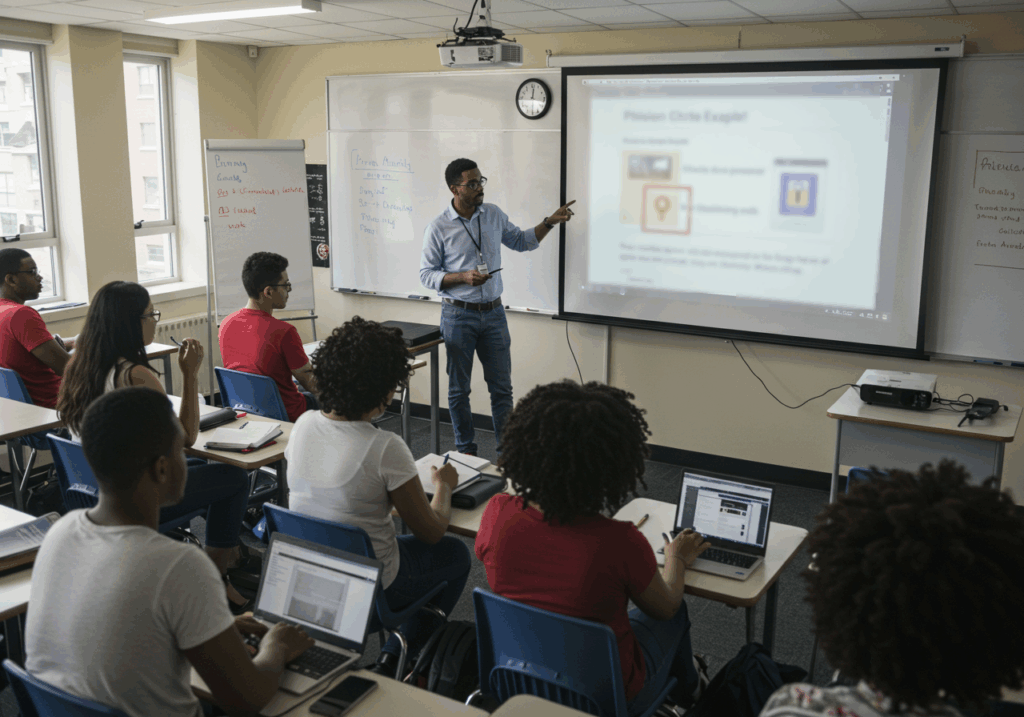
Educating Faculty, Staff, and Students on Cyber Hygiene
Even the most advanced technologies fail if people remain the weakest link. Human behaviour is often the entry point for attacks. Social engineering, phishing, careless credential practices, or the use of insecure devices can undo years of technical hardening.
Why humans remain the weakest link in cybersecurity
Phishing is one of the most common vectors for breaches. Attackers craft believable emails that trick users into clicking on malicious links or revealing credentials. In universities, staff and students may not see themselves as targets, making them more vulnerable to oversight. Studies show significant gaps in cybersecurity awareness and behaviour among students, especially undergraduates. Unless users buy into safe practices, technical controls can be circumvented through social engineering.
Running mandatory awareness and phishing simulation programs
Institutions must run regular cybersecurity awareness training for all constituencies (faculty, staff, students). Topics should include recognizing phishing, use of MFA, safe browsing, device hygiene, use of strong passwords, and reporting incidents. Phishing simulation campaigns help reinforce training, send controlled fake phishing emails, and see who clicks, then follow with remedial training. Over time, measure click rates and improvement. Gamified awareness platforms can boost engagement.
Building a culture of digital responsibility
Safety must be part of the institutional culture. Celebrate “good digital citizens.” Encourage reporting of suspected phishing attempts, near-misses, or security concerns without penalizing honest mistakes. Embed cybersecurity in orientation programs for new students and staff. Peer champions or ambassadors can help spread best practices. Leadership should visibly stress the importance of cybersecurity; when top management models safe digital behaviour, others follow.
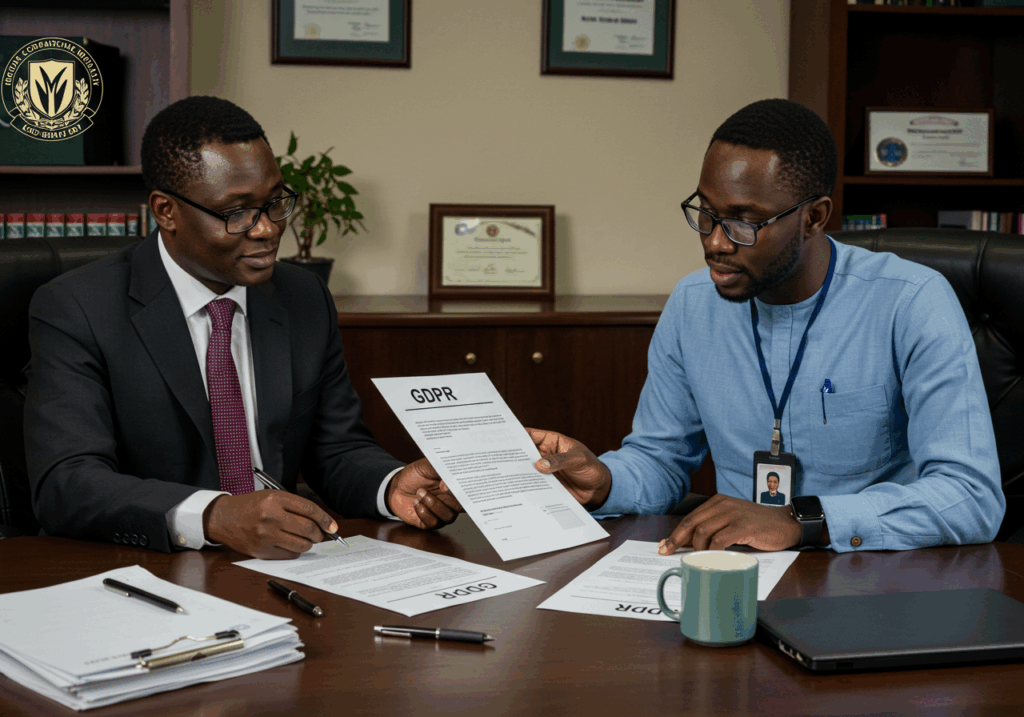
Policy and Compliance: Keeping Universities Secure and Accountable
Technical and human strategies must align with legal, regulatory, and policy frameworks. Institutions that fail on compliance risk fines, reputational damage, or legal exposure.
Nigerian data protection law requirements
Nigeria’s Cybercrimes Act and the Nigeria Data Protection Act (NDPA) set minimum statutory obligations. Under the Cybercrimes Act, it is unlawful to misuse devices or passwords to commit offenses, with penalties ranging from imprisonment to fines. The NDPA and its implementing regulations distinguish between general security incidents and personal data breaches, and mandate duties such as breach notification, appointment of a Data Protection Officer (DPO), and civil liability for harmed data subjects. Institutions must ensure that personal data is processed fairly, securely, and with clear consent or a lawful basis. Violations may lead to enforcement action, fines, or reputational damage.
International standards (GDPR, FERPA), universities should align with
Many universities collaborate internationally with partners subject to the European General Data Protection Regulation (GDPR). Even if not in the EU, it is wise to align practices with GDPR principles (data minimization, purpose limitation, data subject rights). In the U.S., the Family Educational Rights and Privacy Act (FERPA) govern student educational records. Institutions should adopt policy frameworks consistent with such international standards to facilitate collaboration, data sharing, and trust. In addition, ISO/IEC 27001 (information security management) is a widely accepted standard that provides a formal structure for governance, risk assessment, controls, and continual improvement.
How compliance can reduce cyber risks and improve credibility
Compliance drives discipline. Requirements such as regular audits, policy review, access controls, breach response, and logging push institutions to execute good practices. A university that demonstrates compliance becomes more credible to students, funders, and research partners. Moreover, adherence to regulatory obligations gives legal cover and clarity in the event of a breach. A strong compliance posture can also act as a differentiator in a competitive higher education market.
Collaboration and Future Outlook for Academic Cybersecurity
Given the scale and sophistication of threats, universities cannot defend in isolation. Collaboration is crucial.
Partnerships with cybersecurity firms and cloud providers
Universities should partner with firms that specialize in security audits, threat intelligence, and managed services. Cloud providers often offer shared security services, threat monitoring, and tools that smaller institutions might not build themselves. These partnerships raise the level of protection without requiring every campus to build all capabilities in-house.
Cross-university initiatives for cyber defence in Africa
In Africa, universities share common challenges: limited budgets, scarce cybersecurity talent, and similar threat vectors. Regional collaboration, for example, shared threat intelligence platforms, joint training programs, and mutual incident response support, can raise resilience. A coordinated consortium that aggregates resources and incident insights can help detect campaign-level threats faster. Universities might pool resources for a shared security operations centre or regional CERT (Computer Emergency Response Team).
Preparing for future threats like AI-powered attacks
The next frontier includes AI-powered attacks, automated phishing, deepfake impersonation, adversarial exploits, and script generation targeted at vulnerabilities. Institutions must anticipate and defend against threats that adapt faster than manual detection. AI-driven defence systems must evolve to counter AI attacks. Moreover, universities that teach AI and host AI research must secure their research models and IP. As generative AI becomes embedded, safeguarding model integrity and access becomes a new dimension of cybersecurity.
The landscape of cybersecurity in higher education is complex and continuously evolving, but the stakes are too high to ignore. Universities are entrusted with personal, financial, and intellectual assets. Every breach erodes trust, every attack costs resources, and every reputational scar may impact recruitment, partnerships, and funding.
In the end, universities that commit to strong cybersecurity do more than protect data; they earn trust. They signal to students, staff, partners, and communities that they value integrity, confidentiality, and continuity. And by so doing, they build a secure foundation for education’s digital future.

